KRA19, a captivating system, has gained significant attention within the realm of machine learning. Its compelling design allows for exceptional capabilities in areas such as natural language processing. This investigation delves into the core components of KRA19, unveiling its advantages and potential implications.
- Firstly, we will analyze the foundational concepts that shape KRA19's design.
- Next, we will investigate the areas of application where KRA19 achieves its {greatest potential|.
- Finally, we will consider the potential impact of KRA19 on the landscape.
Unveiling the Digital Landscape of KRA19.cc, KRA19.at {
The shadowy realm of KRA19.cc and KRA19.at has long captivated researchers and security experts. These domains, often associated with malicious activities, have become a focal point for analyses into the ever-evolving world of cybercrime.
Dissecting the inner workings of KRA19.cc and KRA19.at requires a multifaceted methodology. It involves analyzing network traffic, pinpointing vulnerabilities, and cooperating with international law enforcement agencies to website bring to light the individuals and organizations behind these domains.
The risks posed by KRA19.cc and KRA19.at are significant. They can range from financial fraud to system disruptions. Understanding the threats associated with these domains is crucial for businesses to enhance cybersecurity.
Examining KRA19: A Cybersecurity Perspective
The emergence of novel cyber threats necessitates a constant adaptation in our cybersecurity strategies. One such threat that has captured significant scrutiny is KRA19, a dangerous code with the potential to generate widespread damage. Understanding its mechanisms is crucial for effective defense. This article delves into the complexities of KRA19, analyzing its capabilities and exploring the best strategies to neutralize its impact on individuals and organizations.
A key characteristic of KRA19 is its capacity to leverage existing vulnerabilities in software. By breaching these protections, KRA19 can obtain sensitive data. This compromise of data privacy can have severe outcomes for both individuals and organizations.
- Additionally, KRA19's elaboration presents a unique challenge to cybersecurity experts. Its ability to adapt over time, making it challenging to detect. This constant transformation requires ongoing investigation and the implementation of new countermeasures.
Deciphering KRA19: The Enigma Behind the URLs
KRA19 has become a trending subject in recent years. This enigmatic code often appears alongside unusual URLs, leaving many users perplexed. Efforts to decipher the meaning behind KRA19 have been limited, adding to its allure and mystery.
- Maybe KRA19 stands for a hidden entity.
- Could it a cutting-edge technology platform?
- On the other hand, KRA19 could simply be a misleading tactic.
Regardless of its true nature, KRA19 has undoubtedly capturedour curiosity of a significant number virtual communities.
Unveiling the Mysteries of KRA19: Exploring Uncharted Regions
KRA19 remains a puzzle, its true nature shrouded in secrecy. Explorers worldwide are eagerly attempting to penetrate its complexities. Theories abound, ranging from extradimensional phenomena to extraterrestrial technologies. As we journey deeper into this uncharted territory, the possibility of revolutionary discoveries grows stronger with each passing day.
KRA19: A Search for Answers in a Web of Uncertainty
K unveil a perplexing phenomenon known as KRA19. This mysterious entity has captured the curiosity of numerous experts. Its source remain shrouded in mystery, leaving a trail of questions in its wake. As we probe deeper into this multifaceted network of uncertainty, we endeavor to uncover the truth behind KRA19.
Evidence are scattered throughout a vast landscape, each revealing a fragment of the complete truth. Nevertheless, the fragments often confound rather than compose a coherent narrative.
- Possibly the answer lies in untapped sources.
- Is it possible that KRA19 exists outside the bounds of our existing knowledge?
- We must continue to search
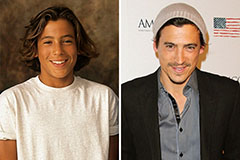 Andrew Keegan Then & Now!
Andrew Keegan Then & Now!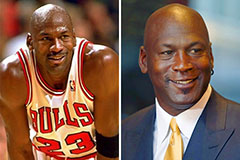 Michael Jordan Then & Now!
Michael Jordan Then & Now!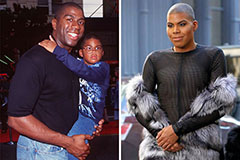 Earvin Johnson III Then & Now!
Earvin Johnson III Then & Now! Monica Lewinsky Then & Now!
Monica Lewinsky Then & Now! Nancy Kerrigan Then & Now!
Nancy Kerrigan Then & Now!